SD-WAN Platform
With a 100% SDN Architecture in the WAN and zero protocol conversion, Lavelle Networks SD-WAN Solution helps you transform legacy MPLS infrastructure to a Safer, Faster and Simpler WAN.
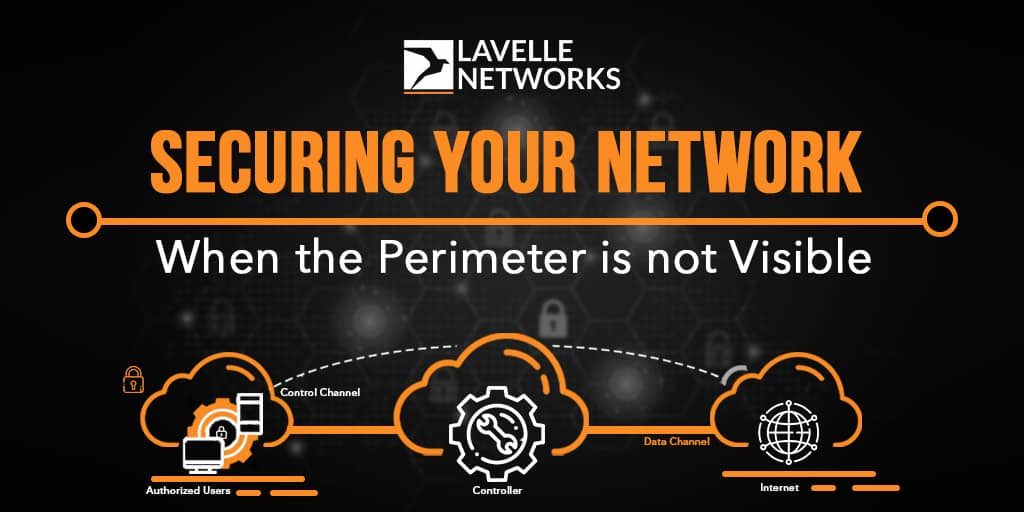
Read MoreBlog » Securing your Network – When the Perimeter is not visible
In the year 1993, a new network function was born – the Firewall. A word which makes IT teams and CIOs smile, grimace and cry. The Network Firewall became like the venerable multi-lever padlock we all learnt to trust for our doors. Until of course it became possible to steal our credit history, personal data, digital assets, and even our cash without bothering to break our lock. The door is well and truly closed, but we worry now not when we lose our keys, but when we lose our…….mobile phone. Because in that phone we have open applications, saved passwords, company credentials, pictures of our family. There is of course one other thing we worry about even when we have our phone……that email from Google or Microsoft warning us that our account seems to be compromised and we should change our password. The aloofness with which cloud & SaaS companies let out press releases that a few million accounts have been hacked (…..but don’t worry we keep everything secure and this breach has helped us make our security better) compounds the worries for our enterprise IT teams.
No wonder, when evangelising SD-WAN, at our customer meetings, we always come across more questions from the CISO and Security teams. Enterprise security has never been easy. And while the venerable Network Firewall did a great job, and still chugs along. I agree, we still need to lock our homes (my cycle recently got stolen when we didn’t), but the thefts at home are more a nuisance. The thefts and attacks on our cloud and device assets are the ones we stay up at night worrying about.
In the last decade, we have seen network appliance and solutions struggle to solve the threesome challenge in Network Security. How does one build a solution where performance, complexity and cost are all solved in the same architecture?
When we pick performance as the criteria, then the appliances become complex and expensive (leading NGFWs). When we pick cost as the criteria, then the appliances are unable to deliver the performance (leading UTMs). And in most cases, managing the security appliance inevitably creates a lot of internal red tape and process ———— the dreaded “firewall port opening” project.
The fundamental issue is that the techniques used in network firewalls have not changed. All firewalls – NGFW or UTM are built using a network traffic inspection engine, where the thesis is to look at as much traffic content as possible to identify that one flow or user or threat which is a real security attack. It’s basically a find the needle in the haystack approach. To make matters worse, the content inspection is hard wired into the firewall software or firmware, which means even if you are an intelligent user and know exactly how to look for the anomaly specific to your application, you cannot do much about it. The second important issue is that all such solutions use a signature or “known pattern” database. These are at times built by in-house teams, but typically 3rd party companies provide the “signature” updates. Our customers at times are then held at ransom for such signature updates, after having been enticed to buy the appliances at a lower cost. The third issue is that the only way we have been asked to manage firewalls is the 25 year old “rule table”. Administrators painstakingly build traffic matching rules to keep out certain traffic and allow certain traffic.
All of this is ok, I mean, even the padlock industry has been moving ahead, we even have digital locks now. But like we established in the beginning, the value of assets we want to secure are now not behind the padlock.
All of us in the technology world remember the [May 2017] time when we were scampering after the news of WannaCryptor broke out. If you want to feel nostalgic about your heroic efforts as the Network Security team, here is a link on what it was about.
One of our partners – a large global technology consulting company, requested an emergency field deployment of SD-WAN to remediate WannaCry in their customer’s network. Ironically, the incident response team was unable to make progress because the existing WAN capacity was insufficient to manage patch upgrades across the network. On an average, the size of the security update issued by Microsoft is about 35MB in size. It keeps changing from Windows version to version.
The details of the security patch are available here. Specifically, if you look at the Microsoft security blog, the title of the article says it all – “WannaCrypt ransomware worm targets out-of-date systems“.
The ugly truth we all were rudely awakened to is that the malware attacks all the systems that have not been patched and are classified as out of date systems. In fact, several of our customers who needed help at that time, were running….shhhhh…..security appliances in their network.
Our discussions with numerous CIOs, CISOs, IT engineers show that there are two end points of modern enterprise application communication, and unless we deploy protection and detection mechanisms for these two, the network security problem cannot be solved. The fact that we are having these discussions, of course, underlines the fact that there is no more disagreement in the industry about why the network firewall exists, and why there is a lot more to do for security than just a firewall.
The first end point is the combination of device, user, credentials, and the application client (most often an app or browser). The second end point is the application server cloud or web service or micro-service (I wanted to say micro service before the developer community throws barbs at us for using old fashioned words like server or service. We also wanted to say containers and Kubernetes but that would be sacrilegious – we will let the application folks debate about that).
Enterprises need a clever, well crafted security architecture to protect, monitor, deflect and secure these two end points. This then needs to be combined to a program of managing the software on these end points and keeping them patched and updated, without worrying about the network bandwidth or availability challenges.
There are hacks and there are solutions. It is time, given the scary and rapid pace at digitisation and cloud migration, that we apply a real 360 degree solution to network security. Simple techniques of looking at content for the odd chance of finding a vulnerability is ok, but we need more.
It is now a well accepted norm that almost every kind of security breach can be detected by looking at what happens to your network before and after the attack. Even the simplest of malware contacts its CnC (Command and Control center) once it is activated from an infected file. In fact, the most often implemented method in a malware sandbox solution is to look for suspicious application process or application NETWORK behaviour when opening an infected file. Network flow analysis using a security lens is an invaluable and inexpensive way to stay on top of your security operations. The challenge thus far though is that the network analytics engines are mostly offline, and either need a sampled traffic or integration using flow record file formats with all your network devices. But when you deploy a cloud powered SD-WAN platform (sorry about the brazen advertising), it becomes possible to analyse all your network flows inline immediately for network behaviour anomaly.
Enterprises are pleasantly surprised at the improved network security they are getting using the power of behaviour analysis of their traffic patterns.
The emerging architecture of SDP (Read our earlier primer on SDP) is solving key challenges for enterprises when it comes to securing their access to the cloud. One of the key problems to solve is to get the user traffic to the SDP cloud network, and here is where the 360 degree architecture of SD-WAN & SDP, is a killer combination. The natural strength of an SD-WAN solution is policy based on-the-fly private network overlays being created from any source to any destination, this allows an enterprise to drop in extremely simple policies to redirect the right traffic to the right SDP gateway. It’s an architecture where you can deploy best of breed networking at your edge using next generation SD-WAN, and you can deploy best of breed security at your cloud using SDP.
Given the astonishing pace of cloud adoption, this will become a water tight and powerful approach to solving the challenges in keeping our networks secure.
This article was authored by Shyamal Kumar, CEO at Lavelle networks and Samuel Natarajan, Chief Security Architect at Lavelle Networks.

SD-WAN Platform
With a 100% SDN Architecture in the WAN and zero protocol conversion, Lavelle Networks SD-WAN Solution helps you transform legacy MPLS infrastructure to a Safer, Faster and Simpler WAN.
Read MoreIs Your Network Slowing Down Application Performance?
Schedule a discussion with our solution consultant. Discuss your networking requirements and the best solution for your needs
Request a Consultation"We Deliver Fastest Transitions from Classical WAN to SD-WAN"
Learn more